Launched in 2006, pfSense is a free and open-source firewall and router software based on FreeBSD. The powerful and easy-to-use, all-in-one solution has become extremely popular and is currently amongst the most trusted open source network security solutions, with millions of installations.
Through its intuitive web interface, pfSense is extremely easy to configure and provides firewall, VPN and routing functionalities that are required for almost all types of network environments. In this article, we’ll take a closer look at the most notable functions of pfSense, the pros and cons of deploying it on bare-metal server vs. virtual machine.
Functionalities of pfSense®
pfSense is a feature-rich and extremely flexible platform, with an extensive range of configurations and a long list of features, which can be further extended through code for additional capabilities. Most frequently utilized for its firewall and routing functions, pfSense offers GeoIP blocking, dynamic DNS, anti-spoofing and concurrent IPv4 and IPv6 support amongst many other features.
Its VPN capabilities include SSL encryption, multiple VPN tunnels, OpenVPN and split tunnelling, whilst pfSense’s comprehensive intrusion prevention system delivers IP blacklist database, layer 7 application detection and Deep Packet Inspection (DPI).
Virtual vs. Hardware
Choosing between virtualizing pfSense and running it on dedicated hardware is something that needs to be considered before you start getting set up. With various advantages to both options, it’s likely to come down to which option works best for your needs.Common considerations when choosing between the two are cost effectiveness, power consumption and security.
Security
A dedicated server will always exceed a Virtual Machine (VM) from a security standpoint, but that doesn�’t necessarily go to say that running pfSense on a virtual machine will cause security vulnerabilities, which ultimately comes down to the overall configuration. Although in theory, virtualizing pfSense is generally considered less secure for instances like server updates to the hypervisor, as well as having your untrusted network directly plugged into your VM platform, by segmenting your network these risks can be greatly reduced.
Efficiency
In terms of efficiency, virtualizing pfSense means utilizing your hardware for maximum efficiency and ultimately saving on energy, power and space. It can be argued that the cost saving benefits far outweigh any potential security risks, which again, if configured correctly, can be avoided. Additionally, by running pfSense on a VM, resources like CPU and memory can be shared and not wasted on a software that will only require a tiny fraction of them the majority of the time.
Scalability
With regards to scalability, running pfSense on a VM also makes it easier to increase and decrease the CPU and memory used. When pfSense is deployed to be used only for creating VPN accounts, the option of a Virtual Machine/Server (VPS) is preferred as one can start with the bare minimum requirements and scale up as the demand for additional VPN accounts grows.
pfSense® Hardware Requirements for Virtual and Dedicated Servers
pfSense software can be deployed in two environments: dedicated hardware and servers with virtualization. Let’s see the requirements needed for each of the two environments.
Minimum pfSense Hardware Requirements for Dedicated Server:
- Quad Core, 64-bit compatible CPU
- 4 GB RAM
- 100 GB Hard Drive
- Dual Port Network Card (Broadcom and Intel work, although we recommend using Intel for best performance and greater throughput)
Minimum pfSense Hardware Requirements for Virtual Server:
- 4 vCPU (make sure the hypervisor has 64-bit compatible CPU)
- 2 GB RAM
- 20 GB Disk
- Broadcom or Intel Network Card
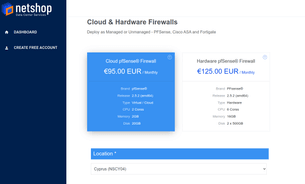
Deploy pfSense® as Virtual or Dedicated Server from €95/mo
Deploy the latest pfSense® software on Cloud or as a Dedicated server. Check out our two plans, choose your desired deployment type, location and you are all set!











![[Updated] Critical cPanel Authentication Vulnerability (28th April 2026) – Immediate Server Update Required](/_gatsby/image/9362bad24aca87aaa90e289c118b76b0/a70bf8734527b8d8f116d23dc89dc569/netshopisp-cpanel-whm-vulnerability-april-2026.png?u=https%3A%2F%2Fnsblg42.netshop-isp.com.cy%2Fwp-content%2Fuploads%2F2026%2F04%2Fnetshopisp-cpanel-whm-vulnerability-april-2026.png&a=w%3D32%26h%3D32%26fm%3Dpng%26q%3D75&cd=7f5f10dc79af53379741259c5c02101d)


